Journal Description
Network
Network
is an international, peer-reviewed, open access journal on science and technology of networks, published quarterly online by MDPI.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, EBSCO, and other databases.
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 18.2 days after submission; acceptance to publication is undertaken in 5.8 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: APC discount vouchers, optional signed peer review, and reviewer names published annually in the journal.
- Network is a companion journal of Electronics.
Latest Articles
An Enhanced Mechanism for Fault Tolerance in Agricultural Wireless Sensor Networks
Network 2024, 4(2), 150-174; https://doi.org/10.3390/network4020008 - 23 Apr 2024
Abstract
►
Show Figures
Fault tolerance is a critical aspect for any wireless sensor network (WSN), which can be defined in plain terms as the quality of being dependable or performing consistently well. In other words, it may be described as the effectiveness of fault tolerance in
[...] Read more.
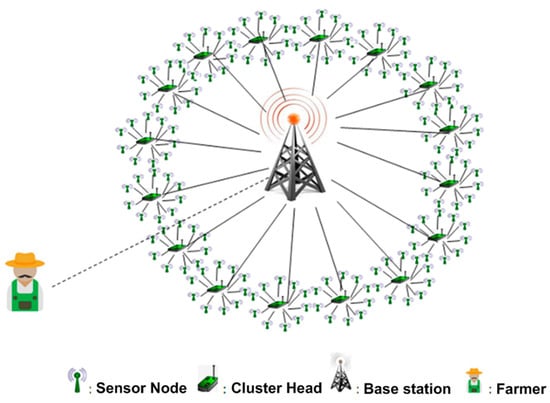
Fault tolerance is a critical aspect for any wireless sensor network (WSN), which can be defined in plain terms as the quality of being dependable or performing consistently well. In other words, it may be described as the effectiveness of fault tolerance in the event of crucial component failures in the network. As a WSN is composed of sensors with constrained energy resources, network disconnections and faults may occur because of a power failure or exhaustion of the battery. When such a network is used for precision agriculture, which needs periodic and timely readings from the agricultural field, necessary measures are needed to handle the effects of such faults in the network. As climate change is affecting many parts of the globe, WSN-based precision agriculture could provide timely and early warnings to the farmers about unpredictable weather events and they could take the necessary measures to save their crops or to lessen the potential damage. Considering this as a critical application area, in this paper, we propose a fault-tolerant scheme for WSNs deployed for precision agriculture. Along with the description of our mechanism, we provide a theoretical operational model, simulation, analysis, and a formal verification using the UPPAAL model checker.
Full article
Open AccessFeature PaperArticle
Medical Data in Wireless Body Area Networks: Device Authentication Techniques and Threat Mitigation Strategies Based on a Token-Based Communication Approach
by
Jan Herbst, Matthias Rüb, Sogo Pierre Sanon, Christoph Lipps and Hans D. Schotten
Network 2024, 4(2), 133-149; https://doi.org/10.3390/network4020007 - 09 Apr 2024
Abstract
Wireless Body Area Networks (WBANs), low power, and short-range wireless communication in a near-body area provide advantages, particularly in the medical and healthcare sector: (i) they enable continuous monitoring of patients and (ii) the recording and correlation of physical and biological information. Along
[...] Read more.
Wireless Body Area Networks (WBANs), low power, and short-range wireless communication in a near-body area provide advantages, particularly in the medical and healthcare sector: (i) they enable continuous monitoring of patients and (ii) the recording and correlation of physical and biological information. Along with the utilization and integration of these (sensitive) private and personal data, there are substantial requirements concerning security and privacy, as well as protection during processing and transmission. Contrary to the star topology frequently used in various standards, the overall concept of a novel low-data rate token-based WBAN framework is proposed. This work further comprises the evaluation of strategies for handling medical data with WBANs and emphasizes the importance and necessity of encryption and security strategies in the context of sensitive information. Furthermore, this work considers the recent advancements in Artificial Intelligence (AI), which are opening up opportunities for enhancing cyber resilience, but on the other hand, also new attack vectors. Moreover, the implications of targeted regulatory measures, such as the European AI Act, are considered. In contrast to, for instance, the proposed star network topologies of the IEEE 802.15.6 WBAN standard or the Technical Committee (TC) SmartBAN of the European Telecommunication Standards Institute (ETSI), the concept of a ring topology is proposed which concatenates information in the form of a ‘data train’ and thus results in faster and more efficient communication. Beyond that, the conductivity of human skin is included in the approach presented to incorporate a supplementary channel. This direct contact requirement not only fortifies the security of the system but also facilitates a reliable means of secure communication, pivotal in maintaining the integrity of sensitive health data. The work identifies different threat models associated with the WBAN system and evaluates potential data vulnerabilities and risks to maximize security. It highlights the crucial balance between security and efficiency in WBANs, using the token-based approach as a case study. Further, it sets a foundation for future healthcare technology advancements, aiming to ensure the secure and efficient integration of patient data.
Full article
(This article belongs to the Special Issue Trustworthy Networking)
►▼
Show Figures
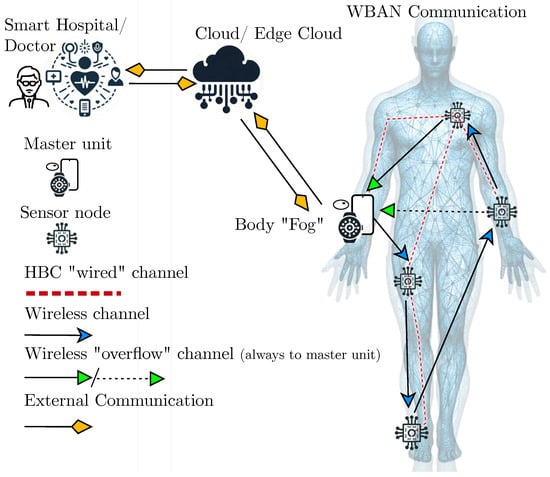
Figure 1
Open AccessArticle
On the Capacity of Optical Backbone Networks
by
João J. O. Pires
Network 2024, 4(1), 114-132; https://doi.org/10.3390/network4010006 - 11 Mar 2024
Abstract
►▼
Show Figures
Optical backbone networks, characterized by using optical fibers as a transmission medium, constitute the fundamental infrastructure employed today by network operators to deliver services to users. As network capacity is one of the key factors influencing optical network performance, it is important to
[...] Read more.
Optical backbone networks, characterized by using optical fibers as a transmission medium, constitute the fundamental infrastructure employed today by network operators to deliver services to users. As network capacity is one of the key factors influencing optical network performance, it is important to comprehend its limitations and have the capability to estimate its value. In this context, we revisit the concept of capacity from various perspectives, including channel capacity, link capacity, and network capacity, thus providing an integrated view of the problem within the framework of the backbone tier. Hence, we review the fundamental concepts behind optical networks, along with the basic physical phenomena present in optical fiber transmission, and provide methodologies for estimating the different types of capacities, mainly using simple formulations. In particular, we propose a method to evaluate the network capacity that relies on the optical reach to account for physical layer aspects, in conjunction with capacitated routing techniques for traffic routing. We apply this method to three reference networks and obtain capacities ranging from tens to hundreds of terabits/s. Whenever possible, we also compare our results with published experimental data to understand how they relate.
Full article
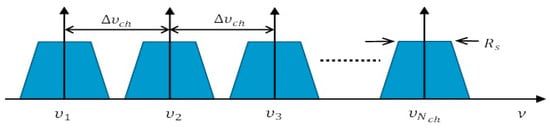
Figure 1
Open AccessArticle
Data Protection Issues in Automated Decision-Making Systems Based on Machine Learning: Research Challenges
by
Paraskevi Christodoulou and Konstantinos Limniotis
Network 2024, 4(1), 91-113; https://doi.org/10.3390/network4010005 - 01 Mar 2024
Abstract
Data protection issues stemming from the use of machine learning algorithms that are used in automated decision-making systems are discussed in this paper. More precisely, the main challenges in this area are presented, putting emphasis on how important it is to simultaneously ensure
[...] Read more.
Data protection issues stemming from the use of machine learning algorithms that are used in automated decision-making systems are discussed in this paper. More precisely, the main challenges in this area are presented, putting emphasis on how important it is to simultaneously ensure the accuracy of the algorithms as well as privacy and personal data protection for the individuals whose data are used for training the corresponding models. In this respect, we also discuss how specific well-known data protection attacks that can be mounted in processes based on such algorithms are associated with a lack of specific legal safeguards; to this end, the General Data Protection Regulation (GDPR) is used as the basis for our evaluation. In relation to these attacks, some important privacy-enhancing techniques in this field are also surveyed. Moreover, focusing explicitly on deep learning algorithms as a type of machine learning algorithm, we further elaborate on one such privacy-enhancing technique, namely, the application of differential privacy to the training dataset. In this respect, we present, through an extensive set of experiments, the main difficulties that occur if one needs to demonstrate that such a privacy-enhancing technique is, indeed, sufficient to mitigate all the risks for the fundamental rights of individuals. More precisely, although we manage—by the proper configuration of several algorithms’ parameters—to achieve accuracy at about 90% for specific privacy thresholds, it becomes evident that even these values for accuracy and privacy may be unacceptable if a deep learning algorithm is to be used for making decisions concerning individuals. The paper concludes with a discussion of the current challenges and future steps, both from a legal as well as from a technical perspective.
Full article
(This article belongs to the Special Issue Next Generation Networks and Systems Security)
►▼
Show Figures
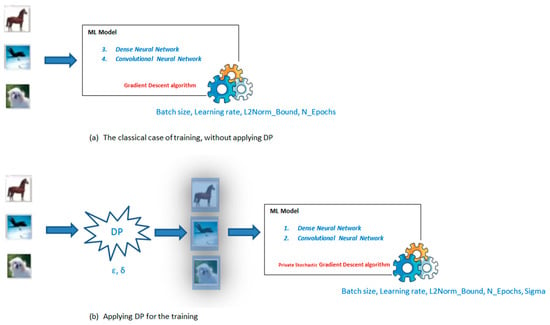
Figure 1
Open AccessArticle
A Hierarchical Security Event Correlation Model for Real-Time Threat Detection and Response
by
Herbert Maosa, Karim Ouazzane and Mohamed Chahine Ghanem
Network 2024, 4(1), 68-90; https://doi.org/10.3390/network4010004 - 11 Feb 2024
Abstract
An intrusion detection system (IDS) perform postcompromise detection of security breaches whenever preventive measures such as firewalls do not avert an attack. However, these systems raise a vast number of alerts that must be analyzed and triaged by security analysts. This process is
[...] Read more.
An intrusion detection system (IDS) perform postcompromise detection of security breaches whenever preventive measures such as firewalls do not avert an attack. However, these systems raise a vast number of alerts that must be analyzed and triaged by security analysts. This process is largely manual, tedious, and time-consuming. Alert correlation is a technique that reduces the number of intrusion alerts by aggregating alerts that are similar in some way. However, the correlation is performed outside the IDS through third-party systems and tools, after the IDS has already generated a high volume of alerts. These third-party systems add to the complexity of security operations. In this paper, we build on the highly researched area of alert and event correlation by developing a novel hierarchical event correlation model that promises to reduce the number of alerts issued by an intrusion detection system. This is achieved by correlating the events before the IDS classifies them. The proposed model takes the best features from similarity and graph-based correlation techniques to deliver an ensemble capability not possible by either approach separately. Further, we propose a correlation process for events rather than alerts as is the case in the current art. We further develop our own correlation and clustering algorithm which is tailor-made to the correlation and clustering of network event data. The model is implemented as a proof of concept with experiments run on standard intrusion detection sets. The correlation achieves an 87% data reduction through aggregation, producing nearly 21,000 clusters in about 30 s.
Full article
(This article belongs to the Special Issue Advanced Technologies in Network and Service Management)
►▼
Show Figures
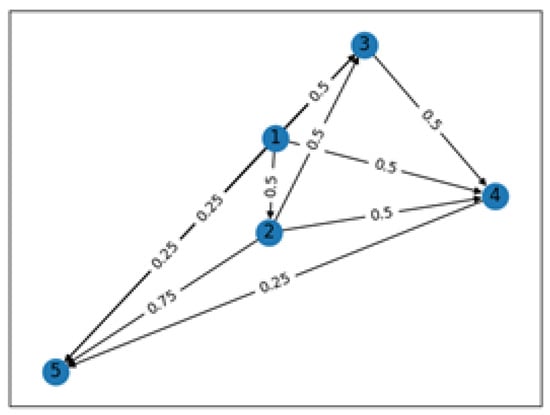
Figure 1
Open AccessArticle
IDSMatch: A Novel Deployment Method for IDS Chains in SDNs
by
Nadia Niknami and Jie Wu
Network 2024, 4(1), 48-67; https://doi.org/10.3390/network4010003 - 07 Feb 2024
Abstract
►▼
Show Figures
With the surge in cyber attacks, there is a pressing need for more robust network intrusion detection systems (IDSs). These IDSs perform at their best when they can monitor all the traffic coursing through the network, especially within a software-defined network (SDN). In
[...] Read more.
With the surge in cyber attacks, there is a pressing need for more robust network intrusion detection systems (IDSs). These IDSs perform at their best when they can monitor all the traffic coursing through the network, especially within a software-defined network (SDN). In an SDN configuration, the control plane and data plane operate independently, facilitating dynamic control over network flows. Typically, an IDS application resides in the control plane, or a centrally located network IDS transmits security reports to the controller. However, the controller, equipped with various control applications, may encounter challenges when analyzing substantial data, especially in the face of high traffic volumes. To enhance the processing power, detection rates, and alleviate the controller’s burden, deploying multiple instances of IDS across the data plane is recommended. While deploying IDS on individual switches within the data plane undoubtedly enhances detection rates, the associated costs of installing one at each switch raise concerns. To address this challenge, this paper proposes the deployment of IDS chains across the data plane to boost detection rates while preventing controller overload. The controller directs incoming traffic through alternative paths, incorporating IDS chains; however, potential delays from retransmitting traffic through an IDS chain could extend the journey to the destination. To address these delays and optimize flow distribution, our study proposes a method to balance flow assignments to specific IDS chains with minimal delay. Our approach is validated through comprehensive testing and evaluation using a test bed and trace-based simulation, demonstrating its effectiveness in reducing delays and hop counts across various traffic scenarios.
Full article

Figure 1
Open AccessArticle
A Study of Ethereum’s Transition from Proof-of-Work to Proof-of-Stake in Preventing Smart Contracts Criminal Activities
by
Oliver J. Hall, Stavros Shiaeles and Fudong Li
Network 2024, 4(1), 33-47; https://doi.org/10.3390/network4010002 - 26 Jan 2024
Abstract
►▼
Show Figures
With the ever-increasing advancement in blockchain technology, security is a significant concern when substantial investments are involved. This paper explores known smart contract exploits used in previous and current years. The purpose of this research is to provide a point of reference for
[...] Read more.
With the ever-increasing advancement in blockchain technology, security is a significant concern when substantial investments are involved. This paper explores known smart contract exploits used in previous and current years. The purpose of this research is to provide a point of reference for users interacting with blockchain technology or smart contract developers. The primary research gathered in this paper analyses unique smart contracts deployed on a blockchain by investigating the Solidity code involved and the transactions on the ledger linked to these contracts. A disparity was found in the techniques used in 2021 compared to 2023 after Ethereum moved from a Proof-of-Work blockchain to a Proof-of-Stake one, demonstrating that with the advancement in blockchain technology, there is also a corresponding advancement in the level of effort bad actors exert to steal funds from users. The research concludes that as users become more wary of malicious smart contracts, bad actors continue to develop more sophisticated techniques to defraud users. It is recommended that even though this paper outlines many of the currently used techniques by bad actors, users who continue to interact with smart contracts should consistently stay up to date with emerging exploitations.
Full article
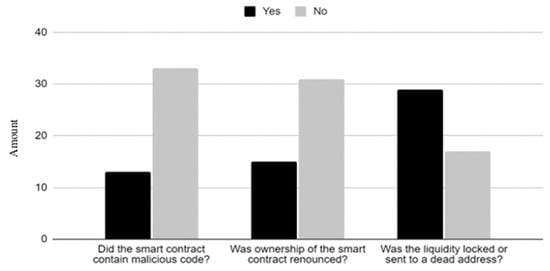
Figure 1
Open AccessReview
A Survey on Routing Solutions for Low-Power and Lossy Networks: Toward a Reliable Path-Finding Approach
by
Hanin Almutairi and Ning Zhang
Network 2024, 4(1), 1-32; https://doi.org/10.3390/network4010001 - 15 Jan 2024
Abstract
►▼
Show Figures
Low-Power and Lossy Networks (LLNs) have grown rapidly in recent years owing to the increased adoption of Internet of Things (IoT) and Machine-to-Machine (M2M) applications across various industries, including smart homes, industrial automation, healthcare, and smart cities. Owing to the characteristics of LLNs,
[...] Read more.
Low-Power and Lossy Networks (LLNs) have grown rapidly in recent years owing to the increased adoption of Internet of Things (IoT) and Machine-to-Machine (M2M) applications across various industries, including smart homes, industrial automation, healthcare, and smart cities. Owing to the characteristics of LLNs, such as Lossy channels and limited power, generic routing solutions designed for non-LLNs may not be adequate in terms of delivery reliability and routing efficiency. Consequently, a routing protocol for LLNs (RPL) was designed. Several RPL objective functions have been proposed to enhance the routing reliability in LLNs. This paper analyses these solutions against performance and security requirements to identify their limitations. Firstly, it discusses the characteristics and security issues of LLN and their impact on packet delivery reliability and routing efficiency. Secondly, it provides a comprehensive analysis of routing solutions and identifies existing limitations. Thirdly, based on these limitations, this paper highlights the need for a reliable and efficient path-finding solution for LLNs.
Full article
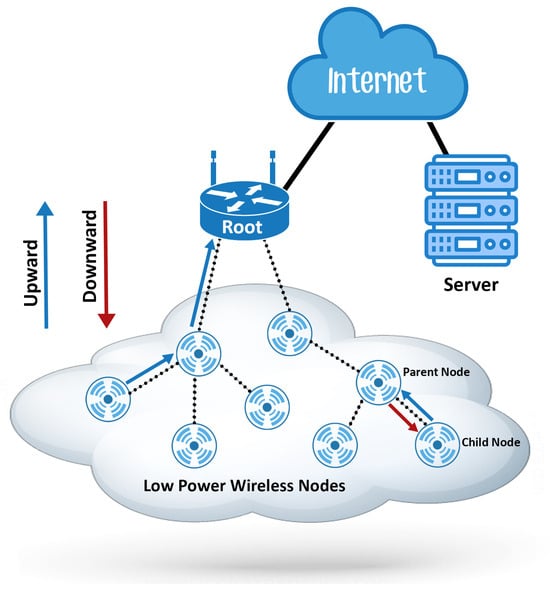
Figure 1
Open AccessReview
TSN Network Scheduling—Challenges and Approaches
by
Hamza Chahed and Andreas Kassler
Network 2023, 3(4), 585-624; https://doi.org/10.3390/network3040026 - 16 Dec 2023
Abstract
►▼
Show Figures
Time-Sensitive Networking (TSN) is a set of Ethernet standards aimed to improve determinism in packet delivery for converged networks. The main goal is to provide mechanisms that enable low and predictable transmission latency and high availability for demanding applications such as real-time audio/video
[...] Read more.
Time-Sensitive Networking (TSN) is a set of Ethernet standards aimed to improve determinism in packet delivery for converged networks. The main goal is to provide mechanisms that enable low and predictable transmission latency and high availability for demanding applications such as real-time audio/video streaming, automotive, and industrial control. To provide the required guarantees, TSN integrates different traffic shaping mechanisms including 802.1Qbv, 802.1Qch, and 802.1Qcr, allowing for the coexistence of different traffic classes with different priorities on the same network. Achieving the required quality of service (QoS) level needs proper selection and configuration of shaping mechanisms, which is difficult due to the diversity in the requirements of the coexisting streams under the presence of potential end-system-induced jitter. This paper discusses the suitability of the TSN traffic shaping mechanisms for the different traffic types, analyzes the TSN network configuration problem, i.e., finds the optimal path and shaper configurations for all TSN elements in the network to provide the required QoS, discusses the goals, constraints, and challenges of time-aware scheduling, and elaborates on the evaluation criteria of both the network-wide schedules and the scheduling algorithms that derive the configurations to present a common ground for comparison between the different approaches. Finally, we analyze the evolution of the scheduling task, identify shortcomings, and suggest future research directions.
Full article
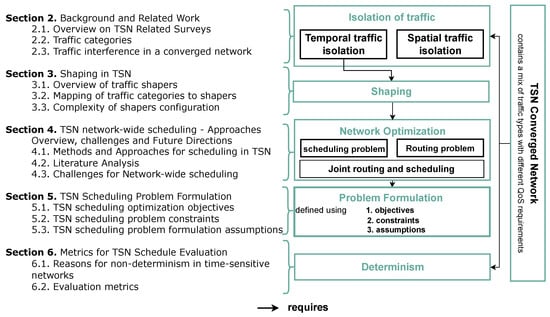
Figure 1
Open AccessReview
Maritime Communications—Current State and the Future Potential with SDN and SDR
by
Nadia Niknami, Avinash Srinivasan, Ken St. Germain and Jie Wu
Network 2023, 3(4), 563-584; https://doi.org/10.3390/network3040025 - 14 Dec 2023
Abstract
►▼
Show Figures
The rise of the Internet of Things (IoT) has opened up exciting possibilities for new applications. One such novel application is the modernization of maritime communications. Effective maritime communication is vital for ensuring the safety of crew members, vessels, and cargo. The maritime
[...] Read more.
The rise of the Internet of Things (IoT) has opened up exciting possibilities for new applications. One such novel application is the modernization of maritime communications. Effective maritime communication is vital for ensuring the safety of crew members, vessels, and cargo. The maritime industry is responsible for the transportation of a significant portion of global trade, and as such, the efficient and secure transfer of information is essential to maintain the flow of goods and services. With the increasing complexity of maritime operations, technological advancements such as unmanned aerial vehicles (UAVs), autonomous underwater vehicles (AUVs), and the Internet of Ships (IoS) have been introduced to enhance communication and operational efficiency. However, these technologies also bring new challenges in terms of security and network management. Compromised IT systems, with escalated privileges, can potentially enable easy and ready access to operational technology (OT) systems and networks with the same privileges, with an increased risk of zero-day attacks. In this paper, we first provide a review of the current state and modalities of maritime communications. We then review the current adoption of software-defined radios (SDRs) and software-defined networks (SDNs) in the maritime industry and evaluate their impact as maritime IoT enablers. Finally, as a key contribution of this paper, we propose a unified SDN–SDR-driven cross-layer communications framework that leverages the existing SATCOM communications infrastructure, for improved and resilient maritime communications in highly dynamic and resource-constrained environments.
Full article
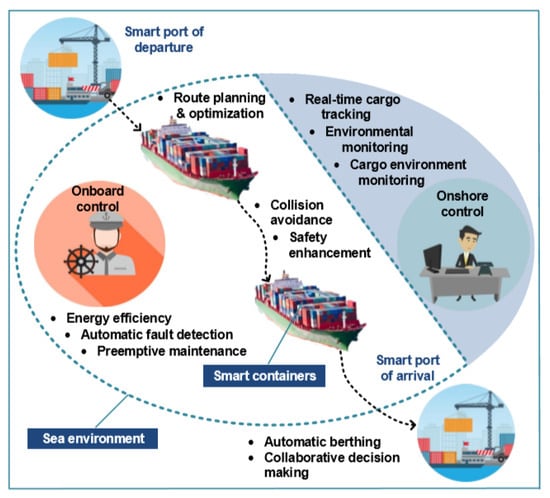
Figure 1
Open AccessArticle
Optimized MLP-CNN Model to Enhance Detecting DDoS Attacks in SDN Environment
by
Mohamed Ali Setitra, Mingyu Fan, Bless Lord Y. Agbley and Zine El Abidine Bensalem
Network 2023, 3(4), 538-562; https://doi.org/10.3390/network3040024 - 01 Dec 2023
Cited by 3
Abstract
In the contemporary landscape, Distributed Denial of Service (DDoS) attacks have emerged as an exceedingly pernicious threat, particularly in the context of network management centered around technologies like Software-Defined Networking (SDN). With the increasing intricacy and sophistication of DDoS attacks, the need for
[...] Read more.
In the contemporary landscape, Distributed Denial of Service (DDoS) attacks have emerged as an exceedingly pernicious threat, particularly in the context of network management centered around technologies like Software-Defined Networking (SDN). With the increasing intricacy and sophistication of DDoS attacks, the need for effective countermeasures has led to the adoption of Machine Learning (ML) techniques. Nevertheless, despite substantial advancements in this field, challenges persist, adversely affecting the accuracy of ML-based DDoS-detection systems. This article introduces a model designed to detect DDoS attacks. This model leverages a combination of Multilayer Perceptron (MLP) and Convolutional Neural Network (CNN) to enhance the performance of ML-based DDoS-detection systems within SDN environments. We propose utilizing the SHapley Additive exPlanations (SHAP) feature-selection technique and employing a Bayesian optimizer for hyperparameter tuning to optimize our model. To further solidify the relevance of our approach within SDN environments, we evaluate our model by using an open-source SDN dataset known as InSDN. Furthermore, we apply our model to the CICDDoS-2019 dataset. Our experimental results highlight a remarkable overall accuracy of 99.95% with CICDDoS-2019 and an impressive 99.98% accuracy with the InSDN dataset. These outcomes underscore the effectiveness of our proposed DDoS-detection model within SDN environments compared to existing techniques.
Full article
(This article belongs to the Special Issue Advanced Technologies in Network and Service Management)
►▼
Show Figures
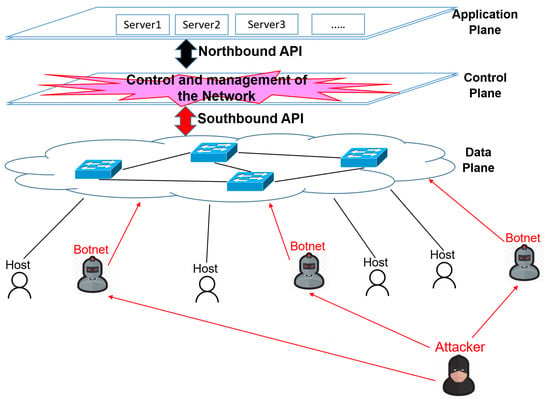
Figure 1
Open AccessArticle
AIS for Malware Detection in a Realistic IoT System: Challenges and Opportunities
by
Hadeel Alrubayyi, Gokop Goteng and Mona Jaber
Network 2023, 3(4), 522-537; https://doi.org/10.3390/network3040023 - 16 Nov 2023
Cited by 1
Abstract
►▼
Show Figures
With the expansion of the digital world, the number of Internet of things (IoT) devices is evolving dramatically. IoT devices have limited computational power and a small memory. Consequently, existing and complex security methods are not suitable to detect unknown malware attacks in
[...] Read more.
With the expansion of the digital world, the number of Internet of things (IoT) devices is evolving dramatically. IoT devices have limited computational power and a small memory. Consequently, existing and complex security methods are not suitable to detect unknown malware attacks in IoT networks. This has become a major concern in the advent of increasingly unpredictable and innovative cyberattacks. In this context, artificial immune systems (AISs) have emerged as an effective malware detection mechanism with low requirements for computation and memory. In this research, we first validate the malware detection results of a recent AIS solution using multiple datasets with different types of malware attacks. Next, we examine the potential gains and limitations of promising AIS solutions under realistic implementation scenarios. We design a realistic IoT framework mimicking real-life IoT system architectures. The objective is to evaluate the AIS solutions’ performance with regard to the system constraints. We demonstrate that AIS solutions succeed in detecting unknown malware in the most challenging conditions. Furthermore, the systemic results with different system architectures reveal the AIS solutions’ ability to transfer learning between IoT devices. Transfer learning is a pivotal feature in the presence of highly constrained devices in the network. More importantly, this work highlights that previously published AIS performance results, which were obtained in a simulation environment, cannot be taken at face value. In reality, AIS’s malware detection accuracy for IoT systems is 91% in the most restricted designed system compared to the 99% accuracy rate reported in the simulation experiment.
Full article
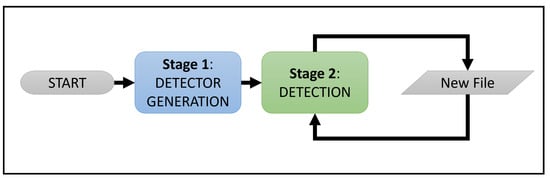
Figure 1
Open AccessArticle
Enhancing Cache Robustness in Information-Centric Networks: Per-Face Popularity Approaches
by
John Baugh and Jinhua Guo
Network 2023, 3(4), 502-521; https://doi.org/10.3390/network3040022 - 01 Nov 2023
Cited by 1
Abstract
►▼
Show Figures
Information-Centric Networking (ICN) is a new paradigm of network architecture that focuses on content rather than hosts as first-class citizens of the network. As part of these architectures, in-network storage devices are essential to provide end users with close copies of popular content,
[...] Read more.
Information-Centric Networking (ICN) is a new paradigm of network architecture that focuses on content rather than hosts as first-class citizens of the network. As part of these architectures, in-network storage devices are essential to provide end users with close copies of popular content, to reduce latency and improve the overall experience for the user but also to reduce network congestion and load on the content producers. To be effective, in-network storage devices, such as content storage routers, should maintain copies of the most popular content objects. Adversaries that wish to reduce this effectiveness can launch cache pollution attacks to eliminate the benefit of the in-network storage device caches. Therefore, it is crucial to protect these devices and ensure the highest hit rate possible. This paper demonstrates Per-Face Popularity approaches to reducing the effects of cache pollution and improving hit rates by normalizing assessed popularity across all faces of content storage routers. The mechanisms that were developed prevent consumers, whether legitimate or malicious, on any single face or small number of faces from overwhelmingly influencing the content objects that remain in the cache. The results demonstrate that per-face approaches generally have much better hit rates than currently used cache replacement techniques.
Full article
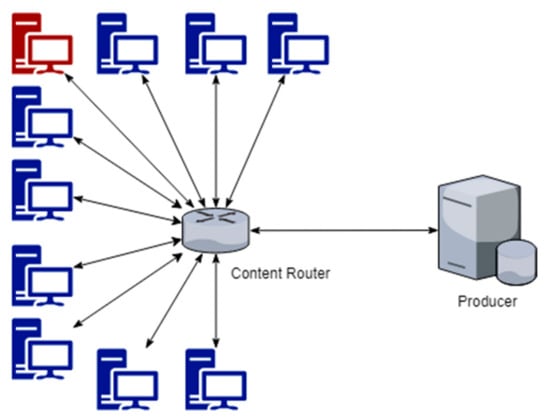
Figure 1
Open AccessFeature PaperArticle
Survey for Soil Sensing with IOT and Traditional Systems
by
Juexing Wang, Xiao Zhang, Li Xiao and Tianxing Li
Network 2023, 3(4), 482-501; https://doi.org/10.3390/network3040021 - 08 Oct 2023
Abstract
Smart Agriculture has gained significant attention in recent years due to its benefits for both humans and the environment. However, the high costs associated with commercial devices have prevented some agricultural lands from reaping the advantages of technological advancements. Traditional methods, such as
[...] Read more.
Smart Agriculture has gained significant attention in recent years due to its benefits for both humans and the environment. However, the high costs associated with commercial devices have prevented some agricultural lands from reaping the advantages of technological advancements. Traditional methods, such as reflectance spectroscopy, offer reliable and repeatable solutions for soil property sensing, but the high costs and redundancy of preprocessing steps limit their on-site applications in real-world scenarios. Recently, RF-based soil sensing systems have opened a new dimension in soil property analysis using IoT-based systems. These systems are not only portable, but also significantly cheaper than traditional methods. In this paper, we carry out a comprehensive review of state-of-the-art soil property sensing, divided into four areas. First, we delve into the fundamental knowledge and studies of reflectance-spectroscopy-based soil sensing, also known as traditional methods. Secondly, we introduce some RF-based IoT soil sensing systems employing a variety of signal types. In the third segment, we introduce the details of sample pretreatment, inference methods, and evaluation metrics. Finally, after analyzing the strengths and weaknesses of the current work, we discuss potential future aspects of soil property sensing.
Full article
(This article belongs to the Special Issue Innovative Mobile Computing, Communication, and Sensing Systems)
►▼
Show Figures
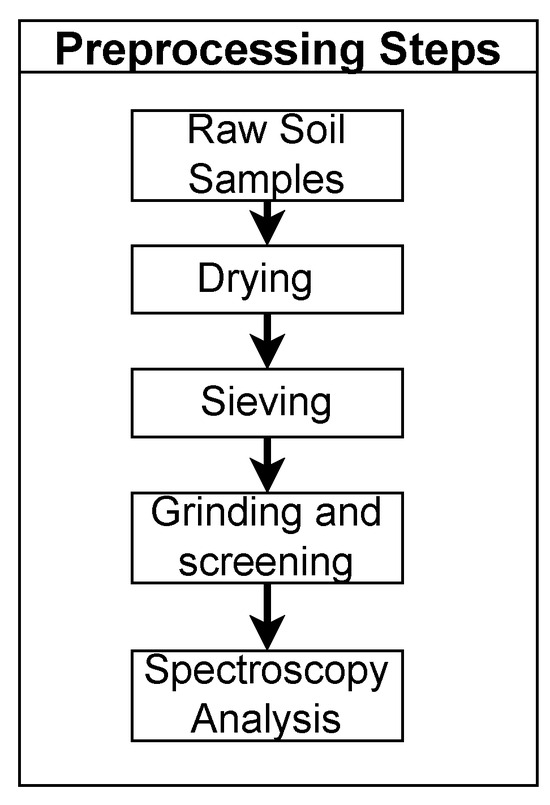
Figure 1
Open AccessArticle
Preventing Black Hole Attacks in AODV Using RREQ Packets
by
Yujin Nakano and Tomofumi Matsuzawa
Network 2023, 3(4), 469-481; https://doi.org/10.3390/network3040020 - 07 Oct 2023
Abstract
►▼
Show Figures
Ad hoc networks, formed by multiple wireless communication devices without any connection to wired or intermediary devices such as by access points, are widely used in various situations to construct flexible networks that are not restricted by communication facilities. Ad hoc networks can
[...] Read more.
Ad hoc networks, formed by multiple wireless communication devices without any connection to wired or intermediary devices such as by access points, are widely used in various situations to construct flexible networks that are not restricted by communication facilities. Ad hoc networks can rarely use existing infrastructure, and no authentication infrastructure is included in these networks as a trusted third party. Hence, distinguishing between ordinary and malicious terminals can be challenging. As a result, black hole attacks are among the most serious security threats to Ad hoc On-demand Distance Vector (AODV) routing, which is one of the most popular routing protocols in mobile ad hoc networks. In this study, we propose a defense method against black hole attacks in which malicious nodes are actively detected to prevent attacks. We applied the proposed method to a network containing nodes engaging in black hole attacks, confirming that the network’s performance is dramatically improved compared to a network without the proposed method.
Full article
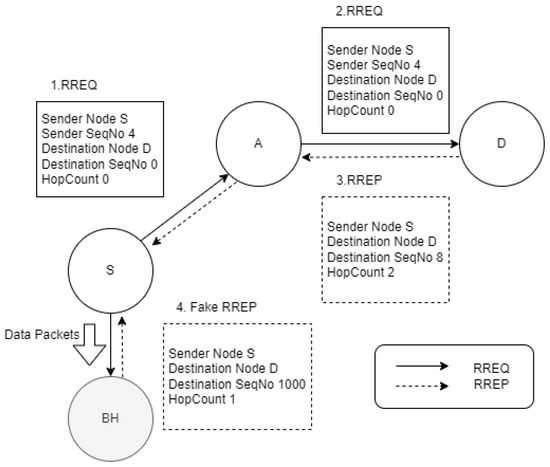
Figure 1
Open AccessArticle
Evaluation of Modern Internet Transport Protocols over GEO Satellite Links
by
Aljuhara Alshagri and Abdulmohsen Mutairi
Network 2023, 3(3), 451-468; https://doi.org/10.3390/network3030019 - 18 Sep 2023
Abstract
►▼
Show Figures
New versions of HTTP protocols have been developed to overcome many of the limitations of the original HTTP/1.1 protocol and its underlying transport mechanism over TCP. In this paper, we investigated the performance of modern Internet protocols such as HTTP/2 over TCP and
[...] Read more.
New versions of HTTP protocols have been developed to overcome many of the limitations of the original HTTP/1.1 protocol and its underlying transport mechanism over TCP. In this paper, we investigated the performance of modern Internet protocols such as HTTP/2 over TCP and HTTP/3 over QUIC in high-latency satellite links. The goal was to uncover the interaction of the new features of HTTP such as parallel streams and optimized security handshake with modern congestion control algorithms such as CUBIC and BBR over high-latency links. An experimental satellite network emulation testbed was developed for the evaluation. The study analyzed several user-level web performance metrics such as average page load time, First Contentful Paint and Largest Contentful Paint. The results indicate an overhead problem with HTTP/3 that becomes more significant when using a loss-based congestion control algorithm such as CUBIC which is widely used on the Internet. Also, the results highlight the significance of the web page structure and how objects are distributed in it. Among the various Internet protocols evaluated, the results show that HTTP/3 over QUIC will perform better by an average of 35% than HTTP/2 over TCP in satellites links specifically with a more aggressive congestion algorithm such as BBR. This can be attributed to the non-blocking stream multiplexing feature of QUIC and the reduced TLS handshake of HTTP/3.
Full article
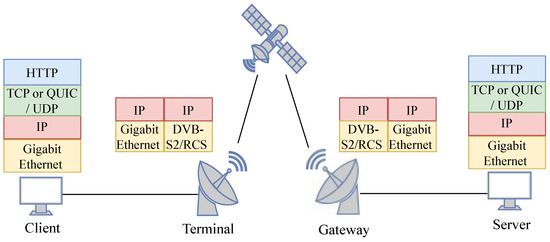
Figure 1
Open AccessReview
An Analysis of Cloud Security Frameworks, Problems and Proposed Solutions
by
Milan Chauhan and Stavros Shiaeles
Network 2023, 3(3), 422-450; https://doi.org/10.3390/network3030018 - 12 Sep 2023
Cited by 6
Abstract
►▼
Show Figures
The rapidly growing use of cloud computing raises security concerns. This study paper seeks to examine cloud security frameworks, addressing cloud-associated issues and suggesting solutions. This research provides greater knowledge of the various frameworks, assisting in making educated decisions about selecting and implementing
[...] Read more.
The rapidly growing use of cloud computing raises security concerns. This study paper seeks to examine cloud security frameworks, addressing cloud-associated issues and suggesting solutions. This research provides greater knowledge of the various frameworks, assisting in making educated decisions about selecting and implementing suitable security measures for cloud-based systems. The study begins with introducing cloud technology, its issues and frameworks to secure infrastructure, and an examination of the various cloud security frameworks available in the industry. A full comparison is performed to assess the framework’s focus, scope, approach, strength, limitations, implementation steps and tools required in the implementation process. The frameworks focused on in the paper are COBIT5, NIST (National Institute of Standards and Technology), ISO (International Organization for Standardization), CSA (Cloud Security Alliance) STAR and AWS (Amazon Web Services) well-architected framework. Later, the study digs into identifying and analyzing prevalent cloud security issues. This contains attack vectors that are inherent in cloud settings. Plus, this part includes the risk factor of top cloud security threats and their effect on cloud platforms. Also, it presents ideas and countermeasures to reduce the observed difficulties.
Full article
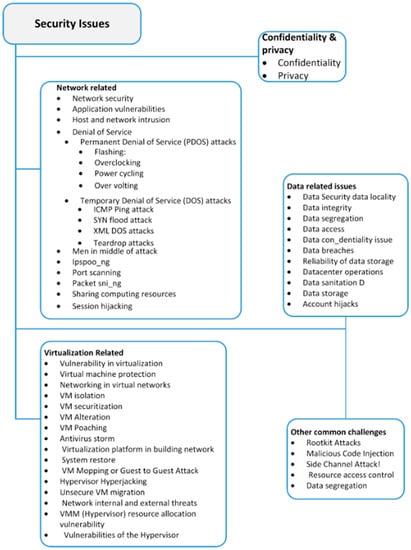
Figure 1
Open AccessReview
A Review of Blockchain Technology in Knowledge-Defined Networking, Its Application, Benefits, and Challenges
by
Patikiri Arachchige Don Shehan Nilmantha Wijesekara and Subodha Gunawardena
Network 2023, 3(3), 343-421; https://doi.org/10.3390/network3030017 - 30 Aug 2023
Cited by 3
Abstract
►▼
Show Figures
Knowledge-Defined Networking (KDN) necessarily consists of a knowledge plane for the generation of knowledge, typically using machine learning techniques, and the dissemination of knowledge, in order to make knowledge-driven intelligent network decisions. In one way, KDN can be recognized as knowledge-driven Software-Defined Networking
[...] Read more.
Knowledge-Defined Networking (KDN) necessarily consists of a knowledge plane for the generation of knowledge, typically using machine learning techniques, and the dissemination of knowledge, in order to make knowledge-driven intelligent network decisions. In one way, KDN can be recognized as knowledge-driven Software-Defined Networking (SDN), having additional management and knowledge planes. On the other hand, KDN encapsulates all knowledge-/intelligence-/ cognition-/machine learning-driven networks, emphasizing knowledge generation (KG) and dissemination for making intelligent network decisions, unlike SDN, which emphasizes logical decoupling of the control plane. Blockchain is a technology created for secure and trustworthy decentralized transaction storage and management using a sequence of immutable and linked transactions. The decision-making trustworthiness of a KDN system is reliant on the trustworthiness of the data, knowledge, and AI model sharing. To this point, a KDN may make use of the capabilities of the blockchain system for trustworthy data, knowledge, and machine learning model sharing, as blockchain transactions prevent repudiation and are immutable, pseudo-anonymous, optionally encrypted, reliable, access-controlled, and untampered, to protect the sensitivity, integrity, and legitimacy of sharing entities. Furthermore, blockchain has been integrated with knowledge-based networks for traffic optimization, resource sharing, network administration, access control, protecting privacy, traffic filtering, anomaly or intrusion detection, network virtualization, massive data analysis, edge and cloud computing, and data center networking. Despite the fact that many academics have employed the concept of blockchain in cognitive networks to achieve various objectives, we can also identify challenges such as high energy consumption, scalability issues, difficulty processing big data, etc. that act as barriers for integrating the two concepts together. Academicians have not yet reviewed blockchain-based network solutions in diverse application categories for diverse knowledge-defined networks in general, which consider knowledge generation and dissemination using various techniques such as machine learning, fuzzy logic, and meta-heuristics. Therefore, this article fills a void in the content of the literature by first reviewing the diverse existing blockchain-based applications in diverse knowledge-based networks, analyzing and comparing the existing works, describing the advantages and difficulties of using blockchain systems in KDN, and, finally, providing propositions based on identified challenges and then presenting prospects for the future.
Full article
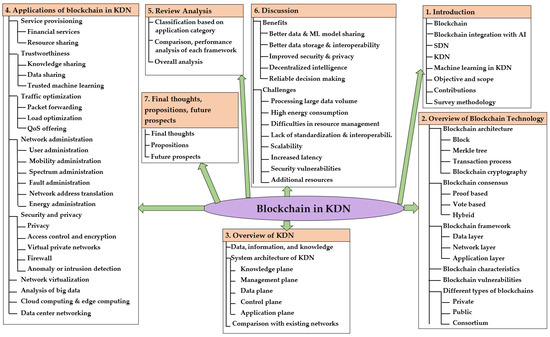
Figure 1
Open AccessFeature PaperArticle
Route Optimization of Unmanned Aerial Vehicle Sensors for Localization of Wireless Emitters in Outdoor Environments
by
Gia Khanh Tran, Takuto Kamei and Shoma Tanaka
Network 2023, 3(3), 326-342; https://doi.org/10.3390/network3030016 - 18 Aug 2023
Cited by 1
Abstract
Localization methods of unknown emitters are used for the monitoring of illegal radio waves. The localization methods using ground-based sensors suffer from a degradation of localization accuracy in environments where the distance between the emitter and the sensor is non-line-of-sight (NLoS). Therefore, research
[...] Read more.
Localization methods of unknown emitters are used for the monitoring of illegal radio waves. The localization methods using ground-based sensors suffer from a degradation of localization accuracy in environments where the distance between the emitter and the sensor is non-line-of-sight (NLoS). Therefore, research is being conducted to improve localization accuracy by utilizing Unmanned Aerial Vehicles (UAVs) as sensors to ensure a line-of-sight (LoS) condition. However, UAVs can fly freely over the sky, making it difficult to optimize flight paths based on particle swarm optimization (PSO) for efficient and accurate localization. This paper examines the optimization of UAV flight paths to achieve highly efficient and accurate outdoor localization of unknown emitters via two approaches, a circular orbit and free-path trajectory, respectively. Our numerical results reveal the improved localization estimation error performance of our proposed approach. Particularly, when evaluating at the 90th percentile of the error’s cumulative distribution function (CDF), the proposed approach can reach an error of 28.59 m with a circular orbit and 12.91 m with a free-path orbit, as compared to the conventional fixed sensor case whose localization estimation error is 55.02 m.
Full article
(This article belongs to the Special Issue Innovative Mobile Computing, Communication, and Sensing Systems)
►▼
Show Figures
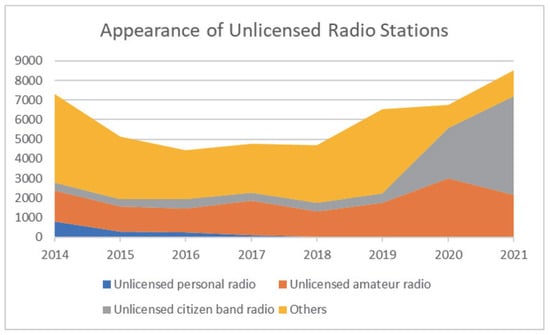
Figure 1
Open AccessArticle
Arithmetic Study about Efficiency in Network Topologies for Data Centers
by
Pedro Juan Roig, Salvador Alcaraz, Katja Gilly, Cristina Bernad and Carlos Juiz
Network 2023, 3(3), 298-325; https://doi.org/10.3390/network3030015 - 26 Jun 2023
Cited by 1
Abstract
Data centers are getting more and more attention due the rapid increase of IoT deployments, which may result in the implementation of smaller facilities being closer to the end users as well as larger facilities up in the cloud. In this paper, an
[...] Read more.
Data centers are getting more and more attention due the rapid increase of IoT deployments, which may result in the implementation of smaller facilities being closer to the end users as well as larger facilities up in the cloud. In this paper, an arithmetic study has been carried out in order to measure a coefficient related to both the average number of hops among nodes and the average number of links among devices for a range of typical network topologies fit for data centers. Such topologies are either tree-like or graph-like designs, where this coefficient provides a balance between performance and simplicity, resulting in lower values in the coefficient accounting for a better compromise between both factors in redundant architectures. The motivation of this contribution is to craft a coefficient that is easy to calculate by applying simple arithmetic operations. This coefficient can be seen as another tool to compare network topologies in data centers that could act as a tie-breaker so as to select a given design when other parameters offer contradictory results.
Full article
(This article belongs to the Special Issue Advances on Networks and Cyber Security)
►▼
Show Figures
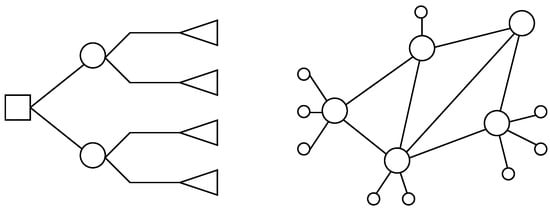
Figure 1
Highly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Applied Sciences, Electronics, IoT, JSAN, Network, Sensors, Telecom, Technologies
Wireless Energy Harvesting and Power Transfer for Communications and Networks
Topic Editors: Yichuang Sun, Arooj Mubashara Siddiqui, Xiaojing Chen, Oluyomi SimpsonDeadline: 31 December 2024

Conferences
Special Issues
Special Issue in
Network
Innovative Mobile Computing, Communication, and Sensing Systems
Guest Editors: Tianxing Li, Nidal NasserDeadline: 30 April 2024
Special Issue in
Network
Next Generation Networks and Systems Security
Guest Editors: Konstantinos Limniotis, Nicholas Kolokotronis, Stavros ShiaelesDeadline: 31 July 2024
Special Issue in
Network
Networking Technologies for Cyber-Physical Systems
Guest Editor: Xinrong LiDeadline: 30 September 2024
Special Issue in
Network
Artificial Intelligence in Effective Intrusion Detection for Clouds
Guest Editor: Stavros ShiaelesDeadline: 31 December 2024